$ vuurmuur -V
Vuurmuur 0.8.1 (using libvuurmuur 0.8.1)
Copyright (C) 2002-2022 Victor Julien et al
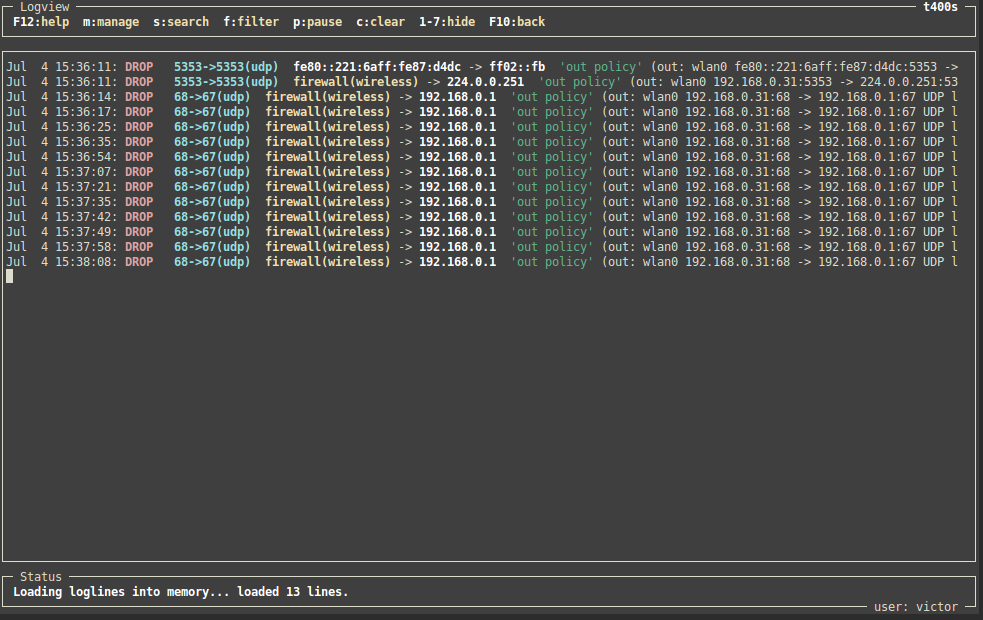
Vuurmuur is a powerful firewall manager built on top of iptables on Linux. It has a simple and easy to learn configuration that allows both simple and complex configurations. The configuration can be fully configured through an Ncurses GUI, which allows secure remote administration through SSH or on the console. Vuurmuur supports traffic shaping, has powerful monitoring features, which allow the administrator to look at the logs, connections and bandwidth usage in realtime. Vuurmuur is open source software and is distributed under the terms of the GNU GPL. Take a look at the list of Features, see the Screenshots for an impression.